Comparing your legacy, aging equipment – your die-hard lathe or CNC milling machine – to new machinery options is easy to do. In fact, there’s a term for it: “appeal to novelty.” Equating newness to superior quality, writes educator Academy 4SC, is a logical fallacy in which something is claimed to be better simply because it is modern. “This is because we assume that people will try to improve upon what came before them. Thus, when we hear about something that’s ‘revolutionary’ or ‘cutting edge,’ it can be tempting to think that this new product is better.”
Centralizing Control
But seasoned maintenance and operations professionals know that aging equipment can perform just as well, running the same hours per day and days per year if maintained properly. And that can translate into exceptional return on investment: one paper mill in Canada had the highest maintenance costs, but was the most profitable, reported Reliable Plant.

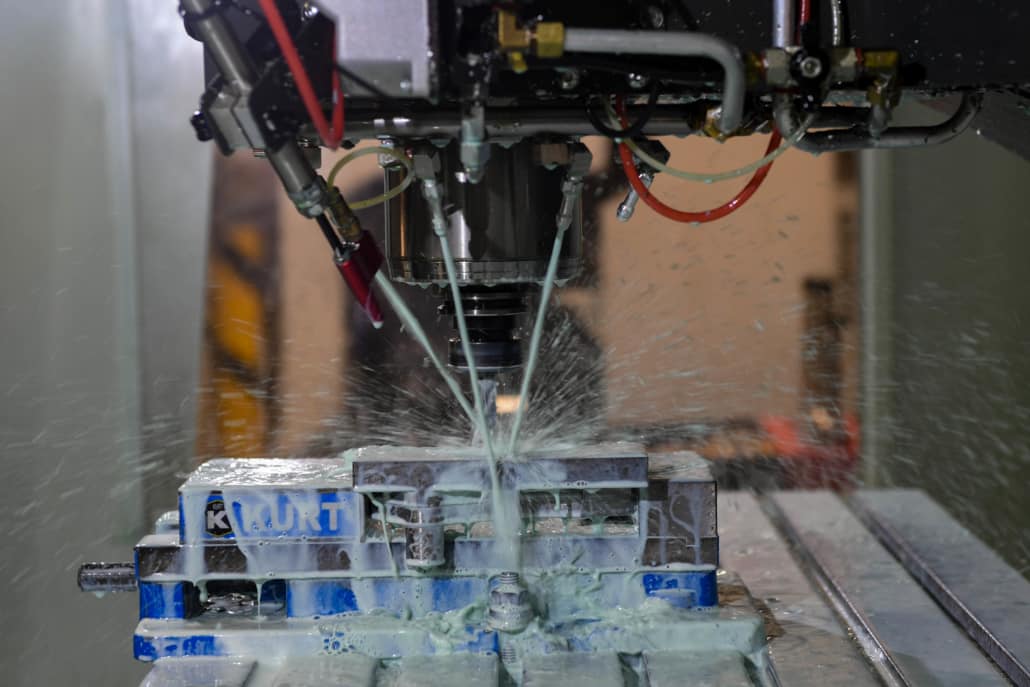
Retrofitting your legacy equipment with the help of a DNC manufacturing integrator can keep manual machines profitable, longer.
The challenge then, can lie in centralizing control of your CNC program and legacy machines, largely due to the vast differences in communication protocols and technology. They may not have built-in networking capabilities or support for modern communications, for example. They will have different data formats and serial communication protocols. And there’s specific troubleshooting and debugging processes associated with older equipment that may require log file analysis, network traffic monitoring, diagnostic tool usage that could vary from machine to machine.
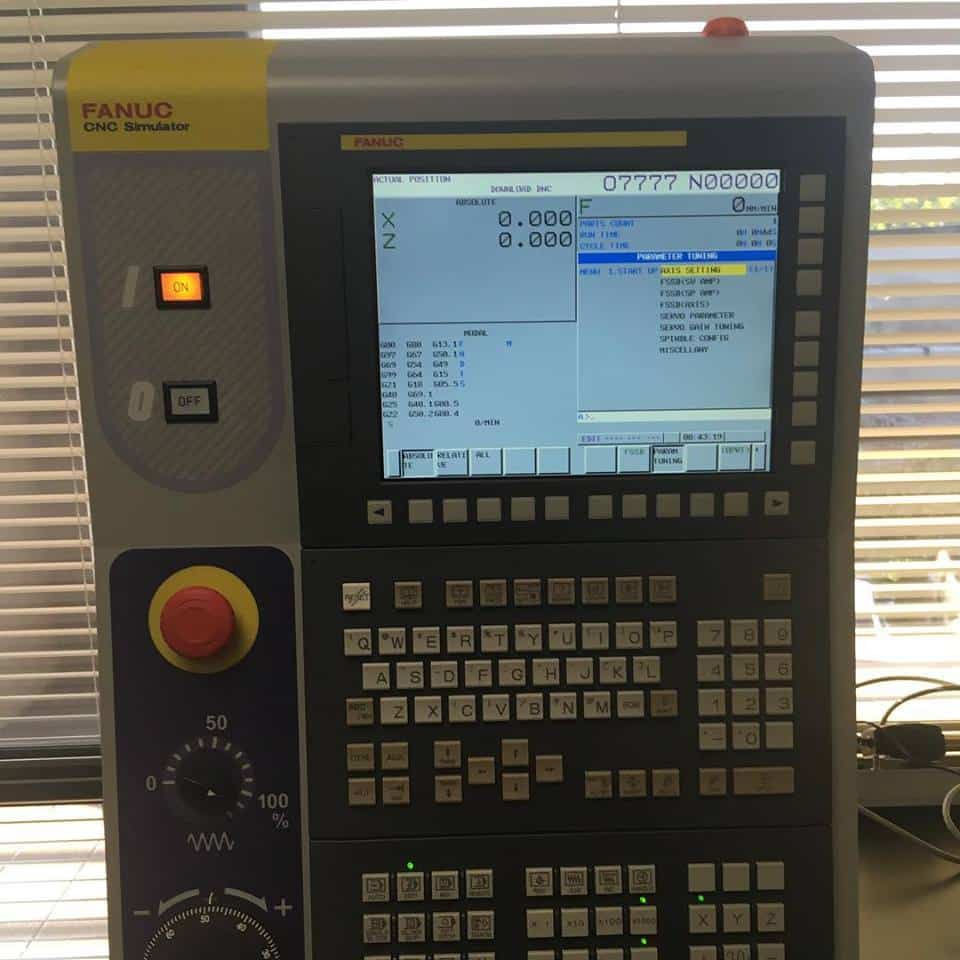
There are options, of course. An ideal Distributed Numerical Control (DNC) software, like Predator DNC, can support over 80 different equipment brands and hundreds of CNC control models to send and receive large NC programs. But software alone won’t be enough to drip feed your CNC programs, control file delivery to the proper CNC machine and monitor the activity of the file transfers to the equipment on the shop floor. There’s still the need to add additional hardware, like serial-to-Ethernet converters, to enable network connectivity.
Your Guide to DNC Manufacturing Integration
That’s where the value of a manufacturing integrator comes in. More than a reseller, a manufacturing integrator has extensive experience using protocols or networking experience that can translate between the protocols used by serial ports on legacy machines. They can provide the DNC software as well as the hardware needed to retrofit or upgrade equipment with newer control systems that interface with the DNC more easily. They have the technical support assistance and large knowledge base of resources, including documentation, FAQs and articles, for instant, on-demand access.
Essentially, a full-service manufacturing integrator has the comprehensive understanding of aging equipment, systems and their respective configurations to design an effective, industrial automation and system integration solution to keep your legacy machines adhering to current processes to keep them profitable longer. To start planning your DNC networking project with an expert DNC manufacturing integrator, contact Shop Floor Automations today.